Cybersecurity: You are the weakest link
Security awareness training is incredibly important to ensure everyone in the company knows what attacks look like, what to do, and what processes to follow. Every person is in charge of their own cybersecurity, both personally and at work.
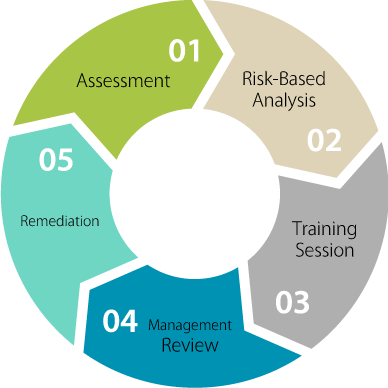
SDAP Security Awareness Training (SAT)
SDAP has hands-on experiences in handling many complicated incident response cases and our certified trainer has over 15 years experiences on information security and is a frequent speaker in many cybersecurity seminars and events.