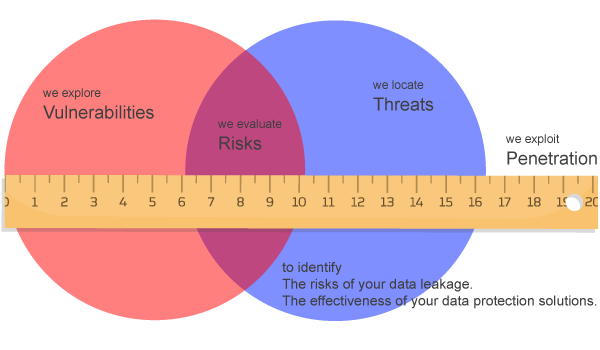
You will find us helpful, because,
We explore vulnerabilities. We locate threats. We evaluate risks. We exploit penetration to identify the risks of your data leakage and the effectiveness of your data protection solution.
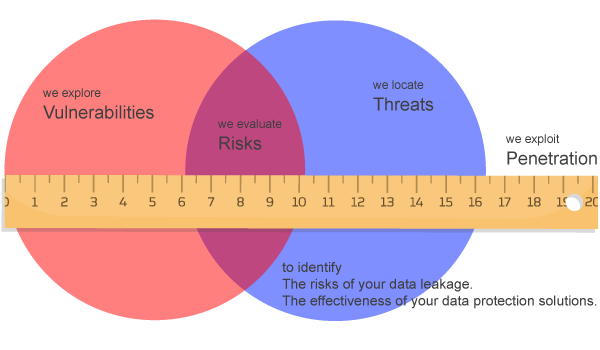
We explore vulnerabilities. We locate threats. We evaluate risks. We exploit penetration to identify the risks of your data leakage and the effectiveness of your data protection solution.
Instead of the traditional IT defensive approach, SDAP takes the offensive approach to search for evidences from the leakage of Data Loss.
In most cases, the victim will not be aware of any sensitive data leakage from their system because the data outflow are not being monitored or well controlled. Movement of data across network boundaries, both electronically and physically, must be scrutinized in order to minimize the risk of data exposure.
We conduct data loss penetration tests for our clients by applying ethical hacking techniques. The evidence and reports from our penetration service will then be reviewed to ensure your company is compliant with Data Loss Protection (DLP).